NS0-603 Online Practice Questions and Answers
You want to manage access to your hybrid cloud resources centrally. You want to use single sign-on (SSO) to access your NetApp Cloud Central accounts using credentials from your corporate directory. Which two open standards would you use to federate your identity to the company's SSO? (Choose two.)
A. Security Assertion Markup Language 2.0 (SAML)
B. Windows Active Directory (AD) authentication protocols
C. Lightweight Directory Access Protocol (LDAP)
D. OpenID Connect (OIDC)
A customer is using AWS for their production environment. One of their applications uploads data into an AWS S3 bucket and the customer wants to duplicate this data into NetApp Cloud Volumes ONTAP. In this scenario, how would the customer copy their data from AWS S3 to Cloud Volumes ONTAP?
A. Use Cloud Backup service.
B. Use SaaS Backup.
C. Use Cloud Tiering.
D. Use Cloud Sync service.
Your customer requires a centralized repository of media files. The repository will be large (in petabytes), with content creators and editors using It from around the globe. They want a NetApp solution that requires minimal administrative resources and provides a good user experience.
In this scenario, which two NetApp technologies would satisfy these requirements? (Choose two.)
A. FlexCache
B. Flash Cache
C. SnapMirror
D. FlexGroup
Exhibit.
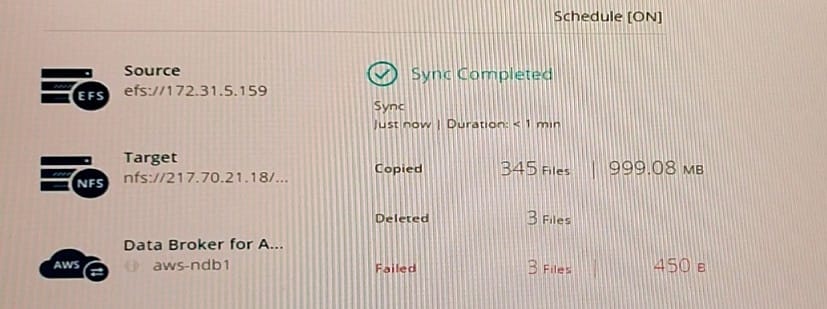
Referring to the exhibit, what are three business reasons for the migration to the new target? (Choose three.)
A. to increase redundancy
B. to refactor the application to use S3 object storage
C. to reduce cost
D. to add NFS v4 support
E. to increase performance
You are sizing a new Azure NetApp Flies deployment and are documenting the throughput limit calculations within the design. In this scenario, which two factors are used to accomplish this task? (Choose two.)
A. the quota that is assigned to the capacity pool
B. the service level of the capacity pool
C. the service level of the volume
D. the quota that is assigned to the volume
You are asked to deploy NetApp Cloud Volumes ONTAP In AWS by using automation tools to help streamline scale and maintain updates. Which two tools would you use to complete this task? (Choose two.)
A. Vagrant
B. Helm
C. Terraform
D. Ansible
You are designing a solution to detect potential insider threats. Your corporate file shares are hosted on NetApp ONTAP arrays.
In this scenario, which two approaches using NetApp cloud services would be appropriate? (Choose two.)
A. Configure Cloud Insights with an Automated Response Policy.
B. Configure Cloud Data Sense service to assign Azure Information Protection (AIP) labels automatically to all files that match the criteria that are defined in a policy.
C. Configure Cloud Backup service for your corporate file share, and ensure that the target is not in the same cloud provider as the source.
D. Configure a Cloud Secure agent with a User Directory Connector.
Which NetApp Cloud Manager feature would be enabled to support Immutability of the data?
A. NetApp Cloud WORM
B. NetApp Storage Encryption
C. NetApp Snapshot
D. NetApp Volume Encryption
Exhibit.
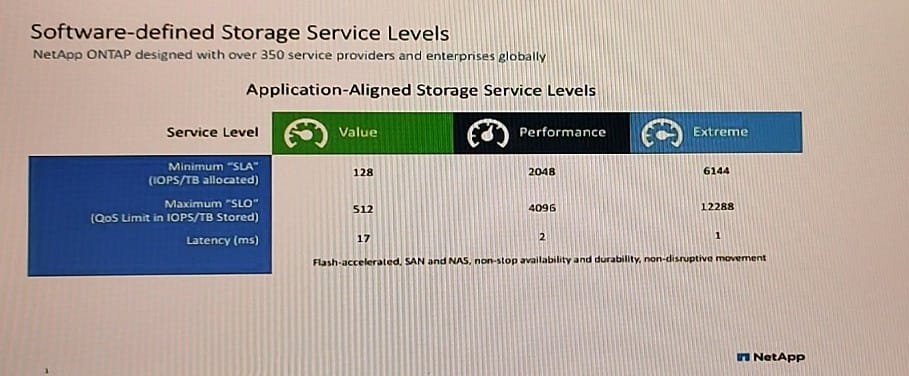
Referring to the exhibit, a volume in the Value storage service level is storing 10 TB of data. What is the maximum number of IOPS that the volume would receive?
A. 1280
B. 5120
C. 128
D. 512
Your company has just merged with another organization. You are responsible for connecting both companies by designing a new multi-region cloud service in Microsoft Azure. Both company's Azure subscriptions and tenants have been merged already. You want to enable cross-region connectivity between the new services and endpoints.
In this scenario, which service do you consider?
A. ExpressRoute
B. VNet Peering
C. Service endpoints
D. Site-to-Site VPN

