CKS Online Practice Questions and Answers
Create a Pod name Nginx-pod inside the namespace testing, Create a service for the Nginx-pod named nginx-svc, using the ingress of your choice, run the ingress on tls, secure port.
A. See explanation below.
B. PlaceHolder
Task Analyze and edit the given Dockerfile /home/candidate/KSSC00301/Docker file (based on the ubuntu:16.04 image), fixing two instructions present in the file that are prominent security/best-practice issues. Analyze and edit the given manifest file /home/candidate/KSSC00301/deployment.yaml, fixing two fields present in the file that are prominent security/best-practice issues.
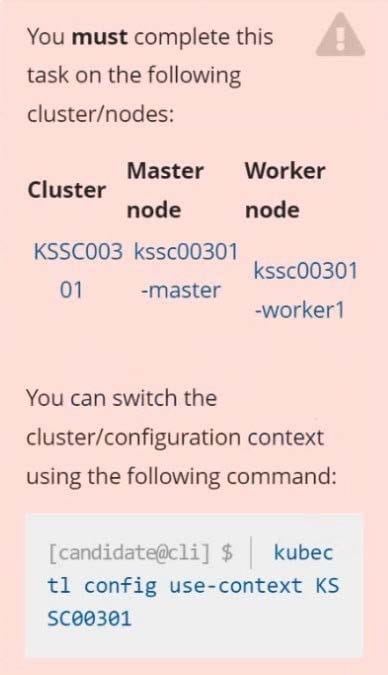
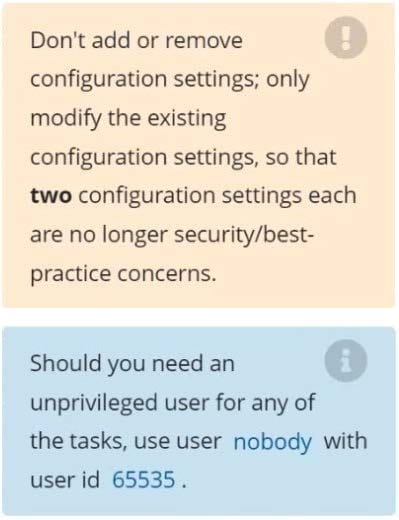
A. See explanation below.
B. PlaceHolder

Fix all issues via configuration and restart the affected components to ensure the new setting takes effect. Fix all of the following violations that were found against the API server:
1.
Ensure that the RotateKubeletServerCertificate argument is set to true.
2.
Ensure that the admission control plugin PodSecurityPolicy is set.
3.
Ensure that the --kubelet-certificate-authority argument is set as appropriate. Fix all of the following violations that were found against the Kubelet:
1.
Ensure the --anonymous-auth argument is set to false.
2.
Ensure that the --authorization-mode argument is set to Webhook. Fix all of the following violations that were found against the ETCD:
1.
Ensure that the --auto-tls argument is not set to true
2.
Ensure that the --peer-auto-tls argument is not set to true
Hint: Take the use of Tool Kube-Bench
A. See the below.
B. PlaceHolder
Create a PSP that will only allow the persistentvolumeclaim as the volume type in the namespace restricted.
Create a new PodSecurityPolicy named prevent-volume-policy which prevents the pods which is having different volumes mount apart from persistentvolumeclaim.
Create a new ServiceAccount named psp-sa in the namespace restricted.
Create a new ClusterRole named psp-role, which uses the newly created Pod Security Policy prevent-volume-policy
Create a new ClusterRoleBinding named psp-role-binding, which binds the created ClusterRole psp-role to the created SA psp-sa.
Hint:
Also, Check the Configuration is working or not by trying to Mount a Secret in the pod maifest, it should get failed.
POD Manifest:
1.
apiVersion: v1
2.
kind: Pod
3.
metadata:
4.
name:
5.
spec:
6.
containers:
7.
- name:
8.
image:
9.
volumeMounts: 10.- name: 11.mountPath: 12.volumes: 13.- name: 14.secret: 15.secretName:
A. See the below:
B. PlaceHolder
You must complete this task on the following cluster/nodes: Cluster: immutable-cluster
Master node: master1
Worker node: worker1
You can switch the cluster/configuration context using the following command:
[desk@cli] $ kubectl config use-context immutable-cluster
Context: It is best practice to design containers to be stateless and immutable.
Task:
Inspect Pods running in namespace prod and delete any Pod that is either not stateless or not immutable.
Use the following strict interpretation of stateless and immutable:
1.
Pods being able to store data inside containers must be treated as not stateless.
Note: You don't have to worry whether data is actually stored inside containers or not already.
2.
Pods being configured to be privileged in any way must be treated as potentially not stateless or not immutable.
A. See the explanation below
B. PlaceHolder
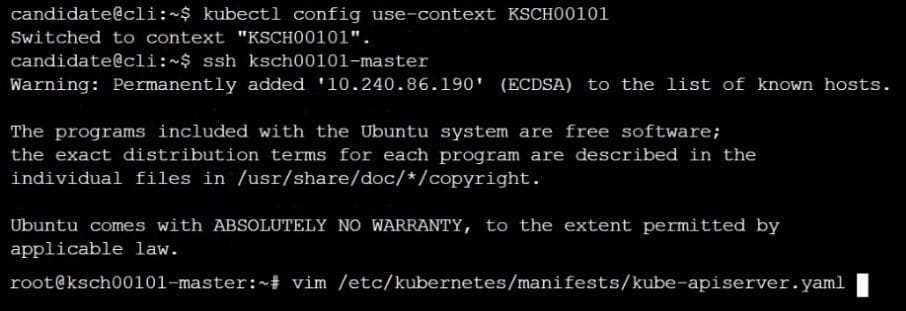
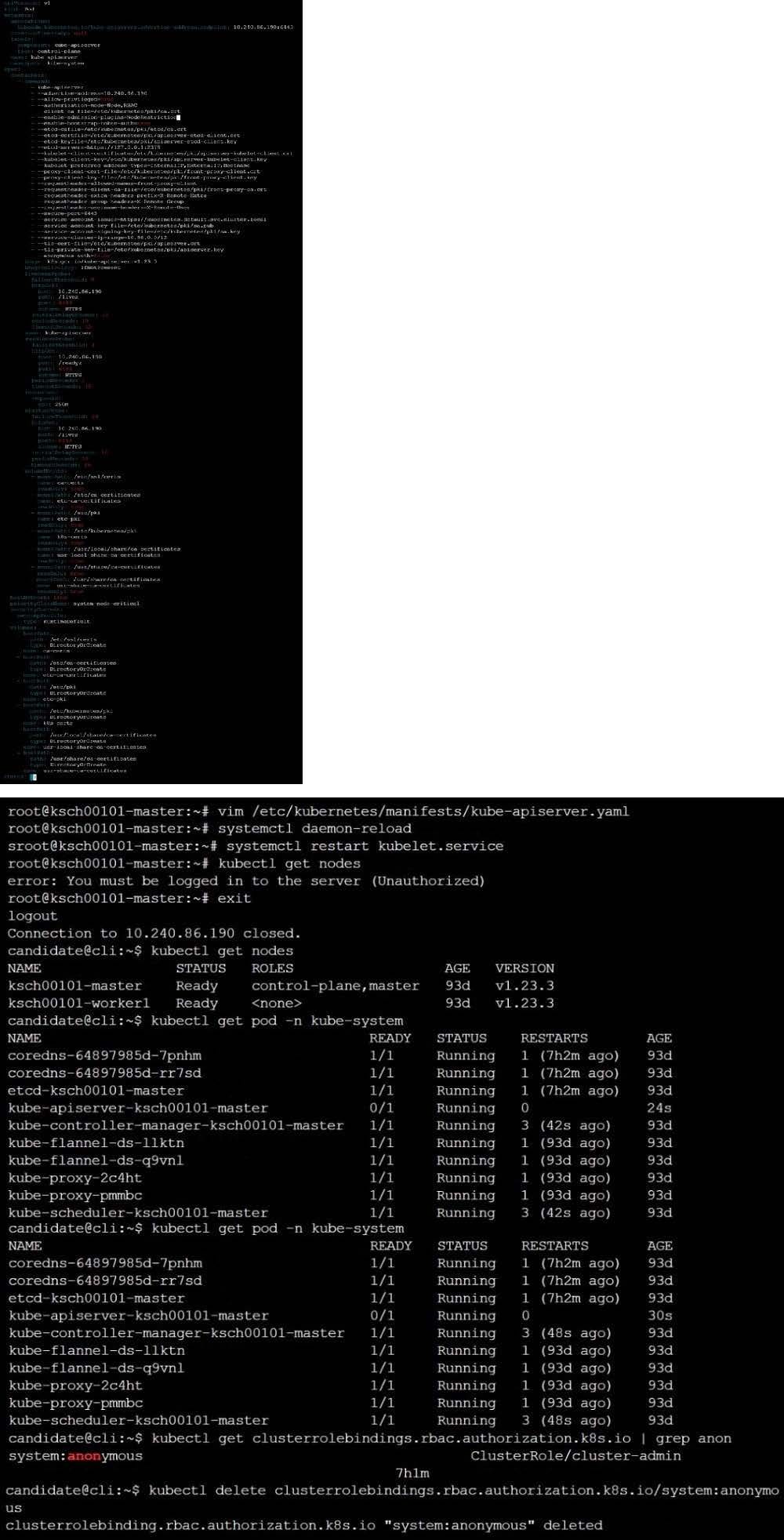
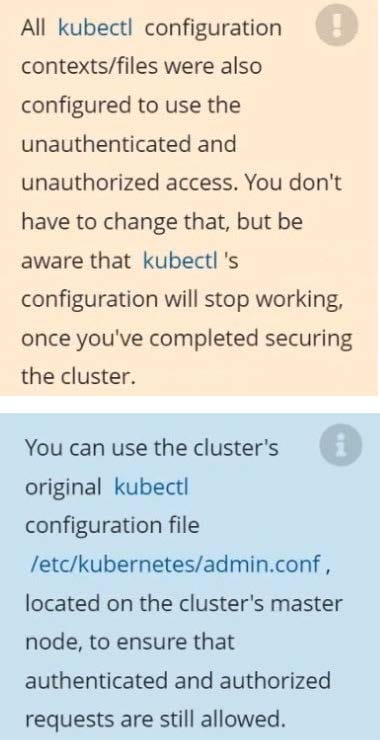
The kubeadm-created cluster's Kubernetes API server was, for testing purposes, temporarily configured to allow unauthenticated and unauthorized access granting the anonymous user duster-admin access.
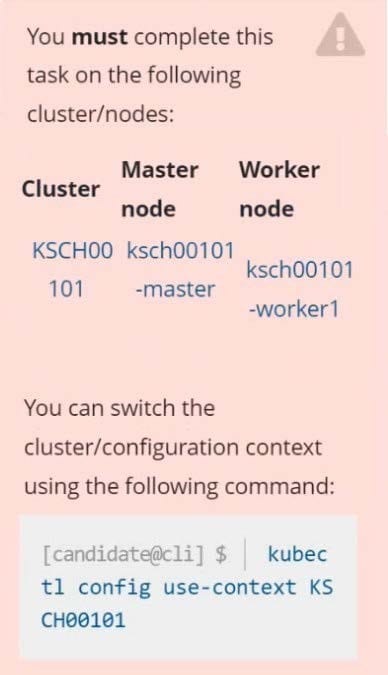
Task
Reconfigure the cluster's Kubernetes API server to ensure that only authenticated and authorized REST requests are allowed.
Use authorization mode Node,RBAC and admission controller NodeRestriction.
Cleaning up, remove the ClusterRoleBinding for user system:anonymous.
A. See explanation below.
B. PlaceHolder
Cluster: qa-cluster
Master node: master Worker node: worker1 You can switch the cluster/configuration context using the following command: [desk@cli] $ kubectl config use-context qa-cluster
Task:
Create a NetworkPolicy named restricted-policy to restrict access to Pod product running in namespace dev.
Only allow the following Pods to connect to Pod products-service:
1.
Pods in the namespace qa
2.
Pods with label environment: stage, in any namespace
A. See the below.
B. PlaceHolder
Create a PSP that will prevent the creation of privileged pods in the namespace.
Create a new PodSecurityPolicy named prevent-privileged-policy which prevents the creation of privileged pods.
Create a new ServiceAccount named psp-sa in the namespace default.
Create a new ClusterRole named prevent-role, which uses the newly created Pod Security Policy prevent-privileged-policy.
Create a new ClusterRoleBinding named prevent-role-binding, which binds the created ClusterRole prevent-role to the created SA psp-sa.
Also, Check the Configuration is working or not by trying to Create a Privileged pod, it should get failed.
A. See the below.
B. PlaceHolder



Context:
Cluster: gvisor
Master node: master1
Worker node: worker1
You can switch the cluster/configuration context using the following command:
[desk@cli] $ kubectl config use-context gvisor
Context: This cluster has been prepared to support runtime handler, runsc as well as traditional one.
Task:
Create a RuntimeClass named not-trusted using the prepared runtime handler names runsc.
Update all Pods in the namespace server to run on newruntime.
A. See the explanation below
B. PlaceHolder

Enable audit logs in the cluster, To Do so, enable the log backend, and ensure that
1.
logs are stored at /var/log/kubernetes-logs.txt.
2.
Log files are retained for 12 days.
3.
at maximum, a number of 8 old audit logs files are retained.
4.
set the maximum size before getting rotated to 200MB
Edit and extend the basic policy to log:
1.
namespaces changes at RequestResponse
2.
Log the request body of secrets changes in the namespace kube-system.
3.
Log all other resources in core and extensions at the Request level.
4.
Log "pods/portforward", "services/proxy" at Metadata level.
5.
Omit the Stage RequestReceived
All other requests at the Metadata level
A. See the explanation below:
B. PlaceHolder