5V0-91.20 Online Practice Questions and Answers
An administrator has configured a policy to run a standard background scan.
How long does this one-time scan take to complete on endpoints assigned to that policy?
A. 180 days
B. 30 days
C. 3-5 days
D. 1 day
What is the meaning, if any, of the event Report write (removable media)?
A. This event would never occur. App Control does not report activity on removable media.
B. A Policy's device control setting `Block writes to unapproved removable media' is set to Report Only. The event details show the process, file name, and hash modified or deleted on the removable media.
C. A Policy's device control setting `Block writes to unapproved removable media' is set to Report Only. The event details show the process and file name modified or deleted on the unapproved removable media.
D. A Policy's device control setting `Block writes to unapproved removable media' is set to Enabled. The event details show the process, file name, and hash modified or deleted on the removable media.
An organization leverages a commonly used software distribution tool to manage deployment of enterprise software and updates. Custom rules are a suitable option to ensure the approval of files delivered by this tool.
Which other trust mechanism could the organization configure for large-scale approval of these files?
A. Windows Update
B. Trusted Distributor
C. Local Approval Mode
D. Rapid Config
An administrator receives an alert with the TTP DATA_TO_ENCRYPTION.
What is known about the alert based on this TTP even if other parts of the alert are unknown?
A. A process attempted to delete encrypted data on the disk.
B. A process attempted to write a file to the disk.
C. A process attempted to modify a monitored file written by the sensor.
D. A process attempted to transfer encrypted data on the disk over the network.
Which two statements are true about Carbon Black alerts? (Choose two.)
A. They can be grouped together.
B. Once received, it can be dismissed in bulk.
C. Once dismissed, the action cannot be undone.
D. Carbon Black does not generate alerts.
E. They are stored for 15 days.
An active compromise is detected on an endpoint. Due to current policies, the compromise was detected but not terminated.
What would be an appropriate action to end the current communication between the device and the attacker?
A. Uninstall the sensor
B. Place the system into bypass mode
C. Place the system into Quarantine D. Remotely scan the endpoint
Refer to the exhibit, noting the circled red dot:
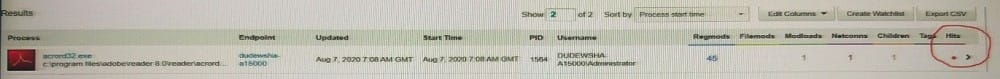
What is the meaning of the red dot under Hits in the Process Search page?
A. Whether the execution of the process resulted in a syslog hit
B. Whether the execution of the process resulted in a sensor hit
C. Whether the execution of the process resulted in matching hits for different users
D. Whether the execution of the process resulted in a feed hit
An administrator needs to manage a group of sensors from within the console.
Which three actions are available for sensors within the Sensor Group? (Choose three.)
A. Move to group
B. Disable
C. Restart
D. Ban
E. Uninstall
F. Share Settings
How can an analyst disregard alerts on multiple devices with the least amount of administrative effort?
A. Select the "Dismiss on all devices" option.
B. Make a note in the Notes/Tags option.
C. Search by hash and dismiss.
D. Turn off the Group Alerts option.
Why would a sensor have a status of "Inactive"?
A. The sensor has not checked in within the last 30 days.
B. The sensor has been uninstalled from the endpoint for more than 30 days.
C. The device has been put in bypass for the last 30 days.
D. The sensor has been in disabled mode for more than 30 days.

